Download sample application updated from previous post - ADFIntegration2.zip. Its the same application described in my previous post, now updated with ADF Security.
I should say, currently there is no elegant approach for ADF Security integration from different applications. Its supposed to be possible to define multiple Policy Stores and declare them in JPS configuration file. I have tried this, however it always using first available Policy Store. Also I was thinking to put jazn-data.xml outside my ADF application, in order to reuse the same jazn-data.xml in multiple applications - but without success. Yes, its possible to specify custom jazn-data.xml file location in JPS configuration file, however current JDeveloper 11g release can't recognize it during design time. Most probably Oracle will fix it in their new JDeveloper 11g build and it will be very easy to split ADF Security across integrated applications. For now, we are using approach to have separate jazn-data.xml per application and in main application jazn-data.xml to store policies from all available jazn-data.xml files. We need to have Policy Stores in splitted applications, since we want to test ADF Security during development cycle.
Will describe how I have applied this approach in my sample application. First, I have configured one of splitted (RemoteSecondApp) application with ADF Security through standard wizard and set permission for ADF Task Flow:

I have declared RemoteSecondApp Policy Store for this application, where security role manager was defined and user scott granted with this role:

In the second splitted application (RemoteApp) I did the same action and declared permissions for ADF Task Flow. In this case, I have assigned to roles with grant to open ADF Task Flow:

Same again, specific Policy Store was defined - RemoteApp and two roles created - manager (scott user) and developer (john user):

Worth to mention, in this Policy Store I have defined permission for Entity Object - preventing unauthorized user from editing data. Its defined on Entity Object and grants permission to edit roles only for manager role:

Now let's see main application - LocalApp. I have defined there Policy Store as well, its called as you can predict - LocalApp. I have defined there new role employee and copied two roles from splitted applications - manager and developer:

I should mention - both users (scott and john) are granted with employee role, it allows them to open entry page from LocalApp application. As I said before, policies from splitted applications are copied there in order to make it work when we will run central application:

We can see grants in jazn-data.xml from central application, where ADF Task Flows imported through ADF Libraries are visible. Those grants are local, copied and read from local jazn-data.xml:

Now we can test ADF Security in both - splitted applications and central one, no difference. When I'm running central application and entering with user granted only developer and employee roles:

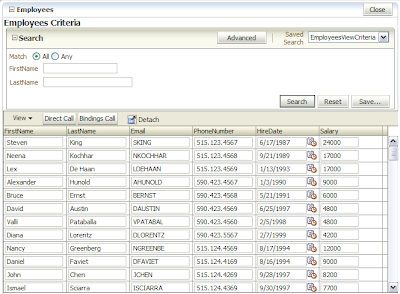
Table from integrated application, where I have declared permission for Entity Object will be rendered in read-only mode:

Since this user don't have permission to open ADF Task Flow from second integrated application, authorization error is shown, thats correct:

When entering with user assigned all roles:

Same table is rendered in editable mode:
5 comments:
I've created few task-flows and introduced security using Jazn.xml, everything works perfectly. But for the task-flows that doesn't have permission, it displays a blank page(in blue background), I need to display some message instead of blank message, please help.
Hi Raza,
Thats strange, it should show Authorization error. May be you have test-all role defined by default for those task flows?
Andrejus
You are true, by default the test-all role is associated to all task-flows. But when I removed it explicitly, it behaves the same. The task flow opens with a blank blue page. It didn't throw any error.
what is the password for scott and jhon users ?
You should use 'welcome1'
Regards,
Andrejus
Post a Comment